2 METHODS · 4 LANGUAGES · 8 VIDEOS
File Anonymization Demos
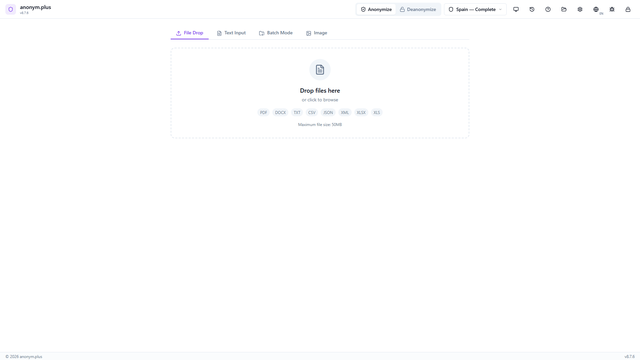
Drop PDF, DOCX, XLSX, CSV, JSON, XML, or TXT files to anonymize entire documents while preserving structure.
File Anonymization (Replace)
Drop documents to anonymize with the Replace operator. PII entities are replaced with type-based placeholders while preserving document structure.
File Anonymization (Replace)
Replace0:41
Dateianonymisierung (Ersetzen)
Replace0:41
Anonimización de Archivos (Reemplazar)
Replace0:41
Anonymisation de Fichiers (Remplacer)
Replace0:41
File Anonymization (Encrypt)
Anonymize documents using AES-256-GCM encryption for reversible file anonymization. Original content can be restored with the encryption key.
File Anonymization (Encrypt)
Encrypt0:41
Dateianonymisierung (Verschlüsseln)
Encrypt0:41
Anonimización de Archivos (Cifrar)
Encrypt0:41
Anonymisation de Fichiers (Chiffrer)
Encrypt0:41
Step-by-Step Process Descriptions
File Anonymization with Replace — Step-by-step guide
- Navigate to the File Drop tab. The dropzone accepts PDF, DOCX, TXT, CSV, JSON, XML, XLSX files up to 50 MB.
- Drop a document file. It appears in a "Ready to Analyze" card with the filename, size, and preset pre-selected. Click "Start Analysis".
- The file card shows "Analyzing..." with a progress bar. Text is extracted and processed through the NER pipeline.
- Review all detected PII entities with color-coded badges and checkboxes.
- Configure the Replace operator for all entity types. Select the output format (same as original, PDF, or DOCX). Click "Anonymize & Save as New File".
- The file is processed and the anonymized output is saved to your output folder.
- Green "Complete" status with entity count displayed. A toast notification confirms the output path.
File Anonymization with Encrypt — Step-by-step guide
- Open the File Drop tab (same dropzone as Replace — supports all document formats up to 50 MB).
- Drop a document file. It appears in "Ready to Analyze" with the preset selected.
- Analysis runs with progress bar while text is extracted and PII detected.
- Review detected entities with color-coded badges.
- Click "All Encrypt" and select an encryption key for reversible encryption.
- The file is processed with encrypt operators and saved to the output folder.
- Output file contains encrypted tokens like <PERSON_ENC:...> that can be decrypted later using the Deanonymize feature.