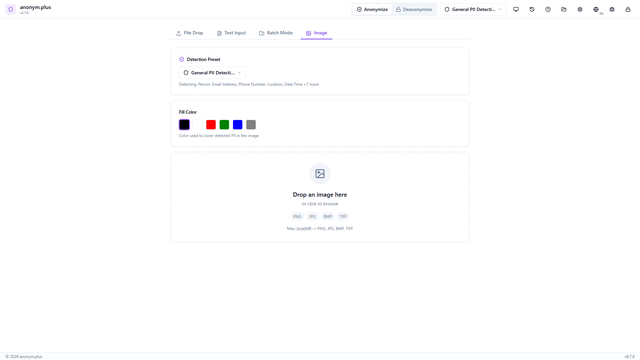
Each video demonstrates a complete anonymization workflow from file drop to export — no narration, no fluff. Every process is shown in four languages (English, German, Spanish, French) with two anonymization methods per category. Use Replace to generate structured placeholders for audit trails, or Encrypt to produce AES-256-GCM ciphertext you can reverse later. All processing happens locally — nothing is uploaded to a server. Browse by category below, or visit individual category pages for the full video playlist.
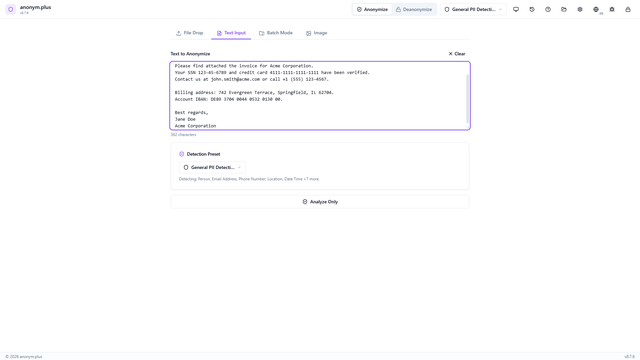
How to use these demos
Each video shows a complete workflow from dropping a file to exporting the anonymized output. Videos are available in English, German, Spanish, and French. Two anonymization methods are demonstrated per category — Replace generates structured placeholder tags for audit trails, while Encrypt produces AES-256-GCM ciphertext that can be fully reversed later using the same key.